What You Do In Protocol Systems
Roles and Protocol Actions
Protocoliday Season continues with an overview of what people do in and around protocol systems. Each of us plays a particular role in each protocol system we inhabit, and the common actions we take in relation to a given system either support or undermine it.
The Protocoliday series lays out the framework of The Protocol System Experience. It provides an analytical foundation that I’m planning to use in posts, interviews, and more in Consider the Human. I’ll use the framework as a tool to examine systems and individual experiences in multiple contexts. (I know that frameworks can be abstract, but I need to tell you the basics so my future work will make sense.)
The below is adapted from my essay The Protocol System Experience, available here.
Now that we have a working definition of protocols and protocol systems (protocols are oughts and a protocol system is a group of people interacting with a protocol), just what is it that people are doing in and around these systems?
Two things: performing a role and taking protocol actions.
Roles
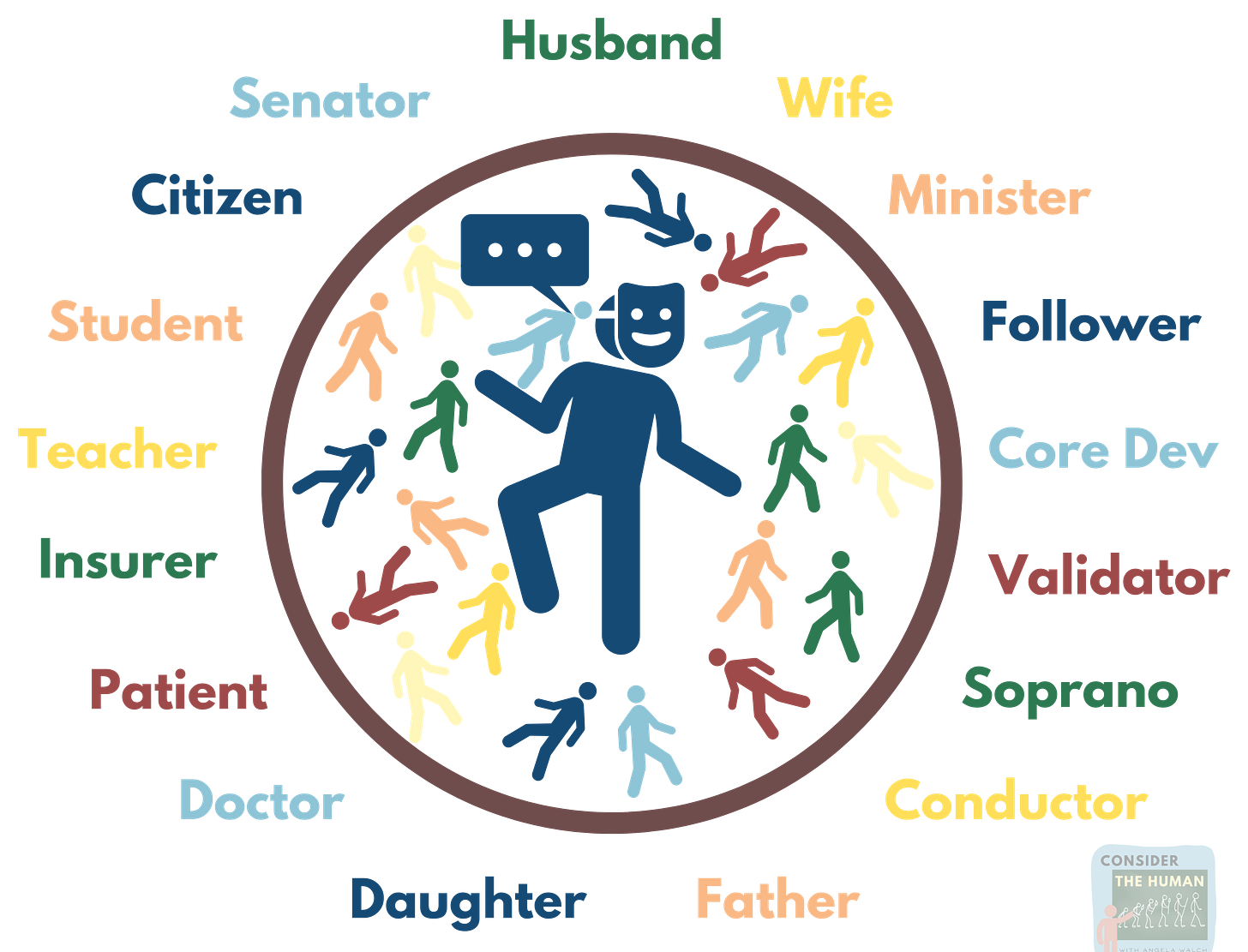
A role is the part a person plays in a protocol system.1 Your role is how you are known to others and it has a name that distinguishes it from other roles within the system. In a family, you may have a parent or child role. In a religion, a minister or a parishioner. In a nation, a president or a citizen. In a blockchain system, a developer, validator, or token holder. Given that we each participate in many protocol systems, each of us “in [our] time plays many parts,”2 some simultaneously and some sequentially.
For each role in a given protocol system, there are expectations—protocols—for how a person in that role should behave, what path they should follow, and how they should relate to others inside and outside the system.3 These protocols may be explicit or implicit. For the role of junior faculty at a university, for example, there are generally written and unwritten rules about what is required to achieve tenure, how to interact with senior faculty, how many university events to attend, what to wear, how much to self-promote, and more. Performing a protocol role successfully yields certain rewards (tenure!), while an unsuccessful performance has negative consequences, potentially including being cast out of the protocol system or even death.4
The role you play within a protocol system has major consequences for your life experience. If you have a role with little power in a protocol system (say, a woman in a patriarchal system), your choices, resources, opportunities, and experiences are very different than if you had a powerful role in the system (say, a man in a patriarchal system).
Sometimes people have the ability to pursue preferences about what role to play in a protocol system (“I want to be vice president of the student council”); in other cases they do not, such as when they are auto-enrolled in roles in protocol systems at birth or during childhood (e.g., when parents assign a default heterosexual role to their young child). Sometimes people believe they are autonomously choosing to join a protocol system and take on a certain role, but don’t realize they are taking this action because their role in a different protocol system requires it, an effect of what I call protocol determinism (e.g., you become a doctor because your role as a daughter in a family protocol system compels you to abide by your parents’ wishes).
We may struggle to see that we are performing a role when we lack awareness of or insight into the relevant protocol system. A role can be mistaken for “who you are” or “your identity,”5 implying that it is a fundamentally unchanging aspect of the self when instead a role is subject to change, rejection, or readoption once a person gains awareness or insight. I’m not developing a full theory here of what constitutes “the self,” (way to big for this series), but I want to draw attention to the felt difference between the internal self and the self presented to the world.
If there is a bad fit between your internal self and your role, you can suffer from a sense of compelled inauthenticity, or dysphoria, while if there is a good fit, and you authentically align with your role, you can thrive. Here, I am borrowing the concept of dysphoria from gender dysphoria, in which there is “a marked incongruence between one’s experienced/expressed gender and their assigned gender” along with “clinically significant distress or impairment in social, occupational, or other important areas of functioning.”6 I think this sense of incongruence (bad fit), distress (dysphoria), and impairment is present not only when there is a mismatch in gender experience and assigned gender, but when there is a mismatch (or bad fit) in any protocol system (whether of the role or the protocol system itself to the person). You can suffer a poor fit and dysphoria in a protocol system whether it is a career, religion, or any other kind. If the role or protocol system feels inalterable, the suffering from dysphoria can be intense, affecting all facets of your life.
Protocol Actions
In addition to performing their roles, people in and around protocol systems perform certain actions that are common across all types of protocol systems. I call these protocol actions.
A protocol action is an action performed in relation to a protocol system that either sustains or weakens that system.
Supportive protocol actions serve to support, grow, or extend the life of a protocol system.
Destructive protocol actions serve to weaken, shrink, or kill off7 a protocol system.
Double-edged protocol actions occupy a middle ground and can be either supportive or destructive depending on the context. Some may help a system grow rapidly but contribute to an early death, while others may foster slow or little growth, but help the system live a long life. These actions are double-edged because when you take them, you are taking a risk on whether they will ultimately help the system or hurt it.
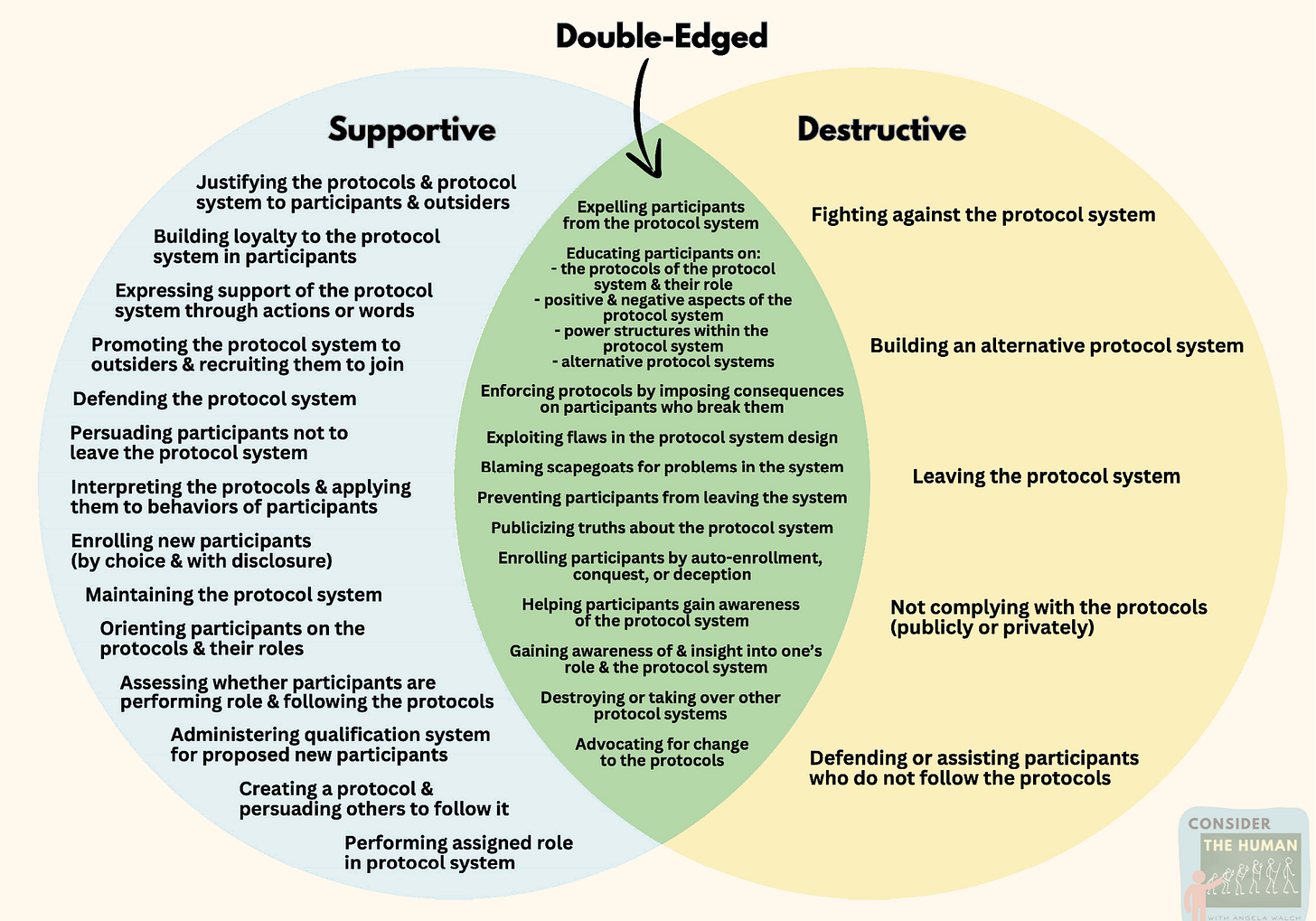
Figure 2 depicts a long list of protocol actions according to whether they are supportive, destructive, or double-edged. A few examples of supportive protocol actions are recruiting new people to join the system, creating loyalty amongst participants, and maintaining the system. Destructive protocol actions include not following the protocols of the system, encouraging participants to leave the system, and publicly criticizing the system. Finally, double-edged protocol actions include actions that could help or hurt the system, depending on the context, such as educating participants and would-be participants of the actual (rather than mythologized) pros and cons of the system, preventing participants from leaving the system, or enrolling new participants through coercion or deception. Forced participation in a system may allow it to grow for a period of time, but if the constraints become too tight, participants ultimately revolt.
Life and Death
Protocol actions are analogous to actions we perform individually to preserve or shorten our own human lives. Supportive life actions would include eating nutritious foods, getting plenty of sleep, and exercising, while destructive life actions would include eating unhealthy food, not getting enough sleep, smoking cigarettes, and not exercising. Double-edged life actions might include working a stressful and demanding but personally meaningful job, losing or gaining a great deal of weight for a movie role, or bearing a child. If not enough supportive life actions are performed, and too many destructive life actions are, death is hastened for the person (as a general rule, though there are certainly exceptions).
If you think about what is necessary to sustain a human life, for instance, you will learn about the need for food, water, air, and protection from the elements, which work to keep the systems of the body operating—the heart beating, the blood pumping, the nervous system sending signals, the filtering systems processing waste, the immune system fighting off invaders, and the digestive system reaping energy from what the body consumes.
If people keep performing supportive protocol actions towards a protocol system, they can keep it alive. If a tipping point occurs where too many people are performing destructive protocol actions, the system heads toward death.
Ultimately, I think a protocol system dies when people stop performing supportive protocol actions in relation to it. This explains why protocol systems must keep taking in new participants to perform supportive protocol actions. For some protocol systems, that may involve having more children who are auto-enrolled in the protocol system (see the “Quiverfull” theory discussed in the Shiny Happy People Amazon docuseries on the Duggar family and their religion8). For others, it may involve taking over other protocol systems or even trying to keep the protocol system alive after early participants have died, through family traditions, practices like primogeniture,9 giving alumni offspring preferences in college admissions, or creating political dynasties like the Kennedys and Bushes.
Many more supportive protocol actions than destructive protocol actions exist, at least by my reckoning, suggesting that protocol systems require lots of tending to form and endure, and that they are vulnerable to a smaller but potent set of destructive protocol functions. However, the long lives of protocol systems such as the Catholic Church or the institution of marriage indicate that certain types of protocol systems can be resilient over centuries.
Good and Bad
People perform supportive and destructive protocol actions in both good and bad protocol systems, if we are rating a protocol system on its moral worth. Just as performing supportive life actions (eating healthy and exercising) can keep a morally flawed person thriving physically, so can supportive protocol actions keep a morally reprehensible protocol system (e.g., slavery) going. Similarly, a morally good person (however defined) can be brought down by destructive life actions (poor diet, isolation, sedentarism) just as a morally good protocol system (e.g., providing healthcare to people) can be destroyed by destructive protocol actions (e.g., exploiting money-making opportunities in the system’s design). Bad protocol systems can live a long time and good ones can die young.
The outcomes that double-edged protocol actions generate seem more aligned with the values/purposes of the protocol system. If truth, openness, and ongoing assessment are values of the system (i.e., are embedded in its protocols), then performing double-edged protocol actions (like truth telling or pointing out issues) may strengthen the system by enabling change (think upward reviews in companies). If truth, openness, and ongoing assessment are not values of the system (perhaps because the protocols bake in power differentials that certain participants benefit from), then performing double-edged protocol actions may keep the system alive for a long time, but may ultimately sign its death warrant when conditions for the less privileged in a protocol system become unendurable.
And there you have it — what people do in protocol systems is play a role and perform protocol actions.
In the next post in this series, we’ll meet the archetypes who inhabit protocol systems: the Guardians, the Threats, the Dualists, the Hierarchics, and the Consciousians. Which have you encountered in your protocol journeys?
I struggled with whether to use role or identity here. Role connotes more of an assigned part to play in a protocol system, while identity connotes an inherent part of the self. As Nadia Asparouhova writes in Dangerous Protocols in protocol systems one’s role can become part of one’s identity, something you associate with who you are. A fundamental aspect of your self. I ultimately chose role for my framework because I want to highlight the possibility of a match or mismatch between the part you play in a protocol system and how you view your self.
William Shakespeare, As You Like It, Jacques in Act II, Scene VII, Line 139.
Other thinkers refer to concepts analogous to protocol roles in domains like sociology, cultural anthropology, social psychology, self-help, economics, game theory, and philosophy.
No, they don’t kill you if you don’t get tenure, but they do cast you out of the university protocol system. Death is a possible consequence in protocol systems that impose the death penalty or engage in honor killings of those who don’t abide by protocols.
Asparouhova also explores this concept in “Dangerous Protocols,” arguing that once a protocol becomes ingrained and unseen (what she calls becoming implicit), people can view their compliance with an (unseen) protocol as part of their very identity.
Diagnostic and Statistical Manual of Mental Disorders, Fifth Edition, Text Revision (DSM-5-TR). American Psychiatric Association. 2022.
I think a protocol system dies when people stop performing supportive protocol actions in relation to the system. Sarah Friend provides insights on protocol death and its process in “Good Death” (Summer of Protocols, 2023).
Mariah Espada, “The True Story Behind the Duggar Family Docuseries Shiny Happy People,” Time, June 2, 2023.
“Primogeniture and ultimogeniture,” Britannica.

I have thought that maturity can almost be defined as “high proficiency in a particular protocol system.” (Chiefly a large scale and nebulous protocol system that overlaps with lots of others.) if you think about it, most times when someone is called immature, the person criticizing is really accusing them of violating one or more protocols. So the accused is alleged to be violating a cardinal “ought” that they “should” know not to break, or at least a “mature” person would know.